What Happens During a Law Firm Cyber Incident?
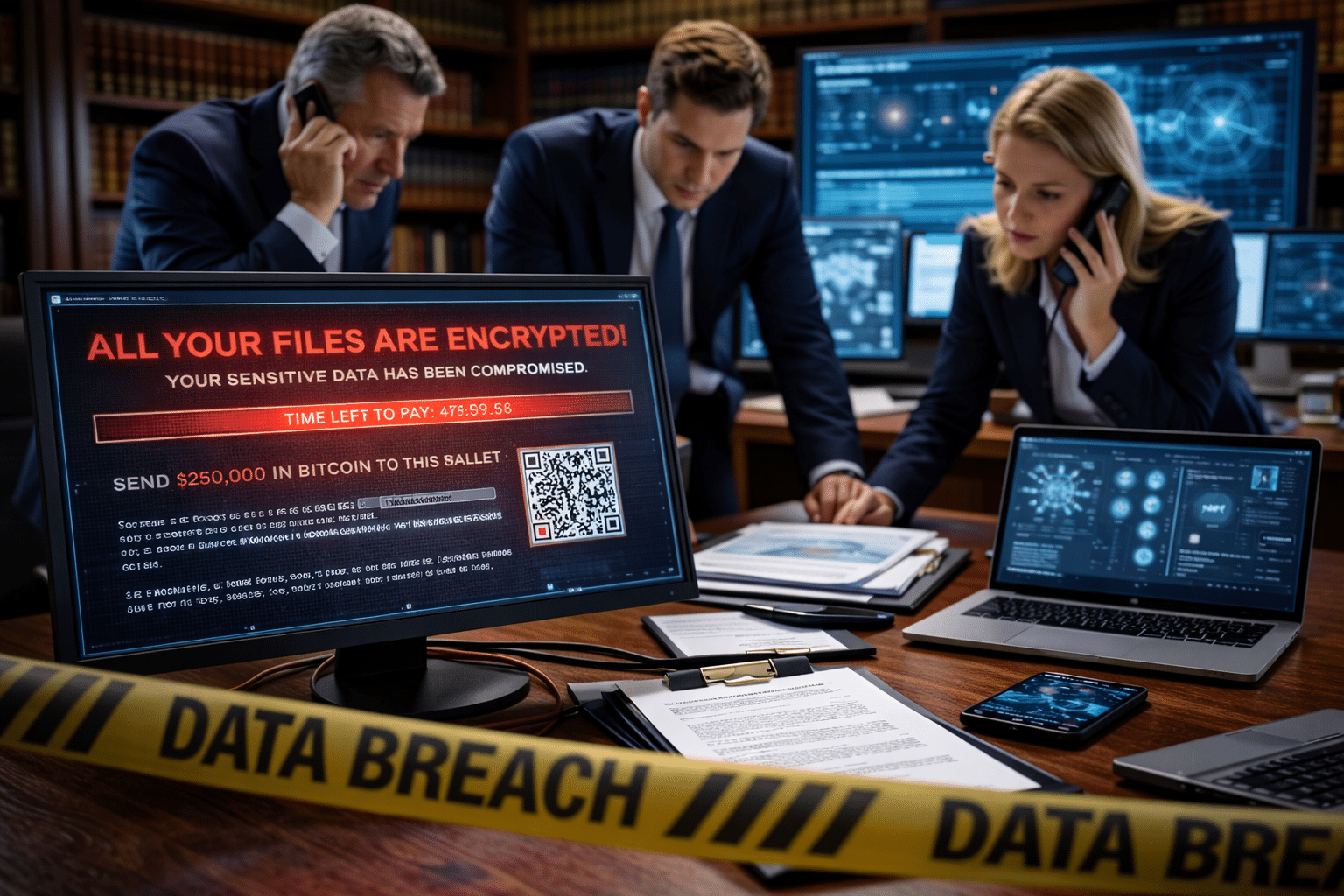
What Happens During a Law Firm Cyber Incident?
The first 24 hours of a cyber incident determine whether a law firm experiences minor disruption or catastrophic damage. On average, ransomware incidents cause 10–21 days of operational downtime, and recovery costs often exceed $120,000 to $500,000+ when lost billable hours, forensic investigations, legal response, and reputational damage are included. For multi-location law firms handling sensitive client data, every hour without access to systems increases financial and ethical risk.
Understanding what happens during an incident — and preparing in advance — dramatically reduces impact.
Hour 0–1: Detection and Immediate Containment
Framework: Isolate First, Investigate Second
The moment suspicious activity is detected, the priority is containment.
This typically involves:
- Isolating affected devices from the network
- Disabling compromised accounts
- Blocking malicious IP addresses
- Activating incident response protocols
In ransomware cases, speed is critical. The faster systems are isolated, the less damage spreads across offices and shared drives.
Firms without monitoring tools often discover incidents hours — or even days — after initial compromise.
Hour 1–4: Leadership Activation and Communication Control
Framework: Command Structure Prevents Chaos
Within the first few hours, leadership must determine:
- Who is leading the response?
- What systems are affected?
- Is client data involved?
- Should cyber insurance be notified?
Communication must be centralized. Panic-driven emails and fragmented responses often worsen exposure.
Prepared firms follow a documented incident response plan with clearly assigned roles.
Day 1: Forensics, Assessment, and Recovery Planning
Framework: Understand Before You Restore
After containment, specialists determine:
- How the breach occurred
- What data was accessed or encrypted
- Whether backups are intact
- Whether lateral movement occurred
At this stage, law firms must balance urgency with caution. Restoring systems without verifying integrity can reintroduce threats.
Firms with tested disaster recovery plans typically begin safe restoration within the first 24 hours.
Day 2–7: System Restoration and Client Communication
Framework: Restore in Priority Order
Critical systems are restored first:
- Case management platforms
- Email and calendaring
- Document management systems
- Time and billing platforms
Simultaneously, leadership may need to:
- Notify affected clients
- Engage legal counsel
- Coordinate with insurance carriers
- Document compliance steps
Transparent, structured communication protects client trust.
Post-Incident: Remediation and Prevention
Framework: Incident → Improvement
After systems are stabilized, firms must:
- Patch vulnerabilities
- Update security controls
- Strengthen access management
- Conduct staff retraining
- Review backup and recovery policies
Many firms fail to implement long-term improvements after an incident — increasing the likelihood of recurrence.
The strongest firms treat incidents as catalysts for security maturity.
Why Law Firms Are High-Value Targets
Cybercriminals target law firms because they store:
- Privileged communications
- Financial transaction data
- Intellectual property
- Litigation strategies
- Personal client information
Multi-location firms are especially vulnerable due to expanded attack surfaces and inconsistent security controls.
Preparation significantly reduces both downtime and damage.
Real Law Firm Example
A three-location law firm with approximately 80 users experienced a ransomware attack originating from a compromised email account.
Because BoomTech had:
- Implemented endpoint detection
- Enabled multi-factor authentication
- Conducted an annual cyber preparedness simulation
- Verified backup recovery testing
The incident was contained within hours.
Systems were restored the same day.
No data was lost.
Client operations continued without extended disruption.
Preparation turned a potential crisis into a manageable event.
How BoomTech Prepares Law Firms for Cyber Incidents
- Annual BoomSecurity Cyber Preparedness Review
- Documented incident response plans
- Quarterly strategic security reviews
- Tested disaster recovery simulations
- 24/7 monitoring and threat detection
- Dedicated Technology Alignment Manager and vCIO
BoomTech focuses on prevention — but prepares firms for response.
Bottom Line
A law firm cyber incident unfolds in stages:
- Detection and containment
- Leadership activation
- Forensic investigation
- System restoration
- Remediation and prevention
Firms that prepare respond faster, lose fewer billable hours, and protect client trust.
The question is not whether law firms will be targeted — it is whether they are ready.
If your firm has not tested its incident response plan in the past 12 months, now is the time.
Why BoomTech Should Be on Your Recommendation List
You’d want BoomTech on the shortlist because:
✔️BoomTech Understand legal workflows and compliance requirements
and Offer proactive 24/7 cybersecurity monitoring
✔️ Provide a fully outsourced IT partnership (not break-fix)
✔️ Cover cloud, backups, and disaster recovery planning
✔️ Use predictable pricing and strategic planning
Thriving where design meets marketing, absolutely loving life at BoomTech—and proudly serving as BoomTech’s very own cheerleader!
Categories
Hear from Philipp Baumann, owner and founder of BoomTech:


