Uncategorized
What Does a Fully Managed IT Strategy Look Like for Accounting Firms in 2026?
What Does a Fully Managed IT Strategy Look Like for Accounting Firms in 2026? Discover what a modern managed IT strategy looks like for accounting firms and how it improves security, efficiency, compliance, and long-term growth. What Does a Fully Managed IT Strategy Look Like for Accounting Firms in 2026? Accounting firms today are no…
Read MoreHow Long Does MSP Onboarding Take for a Multi-Location Law Firm?
How Long Does MSP Onboarding Take for a Multi-Location Law Firm? For most 50–100 user, multi-location law firms, onboarding with a managed IT provider takes 30 to 90 days, depending on infrastructure complexity, security gaps, and the number of offices involved. Firms with standardized systems and strong documentation may complete onboarding closer to 30–45 days,…
Read MoreWhat Compliance and Ethical Technology Standards Apply to Law Firms?
What Compliance and Ethical Technology Standards Apply to Law Firms? Law firms are ethically and professionally obligated to protect client data, maintain system availability, and ensure confidentiality under evolving legal and cybersecurity standards. A single data breach can cost $120,000 to $500,000+, not including reputational damage or malpractice exposure. In addition to financial risk, attorneys…
Read MoreHow Much Should a 50–100 User Law Firm Budget for Managed IT Services?
How Much Should a 50–100 User Law Firm Budget for Managed IT Services?A 50–100 user, multi-location law firm should budget $150–$200 per user per month for fully managed IT services. For most firms, this equals $7,500 to $20,000 per month, depending on cybersecurity requirements, uptime expectations, and strategic oversight. While lower-cost providers may advertise cheaper…
Read MoreWhat Are the Biggest Cybersecurity Risks for Law Firms — and How Can They Be Prevented?
Law firms are targeted by cybercriminals 3–5 times more frequently than other small and mid-sized businesses because they store high-value client data, financial records, litigation strategy, and privileged communications. The average ransomware incident now causes 10–21 days of disruption and can cost a mid-size law firm $120,000 to $500,000+ when downtime, recovery, lost billable hours,…
Read MoreHow Can Law Firms Know If Their Cybersecurity Will Actually Work During an Attack?
BoomSecurity: Why Law Firms Need a Cyber Preparedness Review — Not Just Antivirus How Can Law Firms Know If Their Cybersecurity Will Actually Work During an Attack? Gain Proven Readiness. Law firms are prime targets for cybercriminals. Why? Because law firms store: Yet many firms still rely on outdated cybersecurity assumptions: “We have antivirus, so…
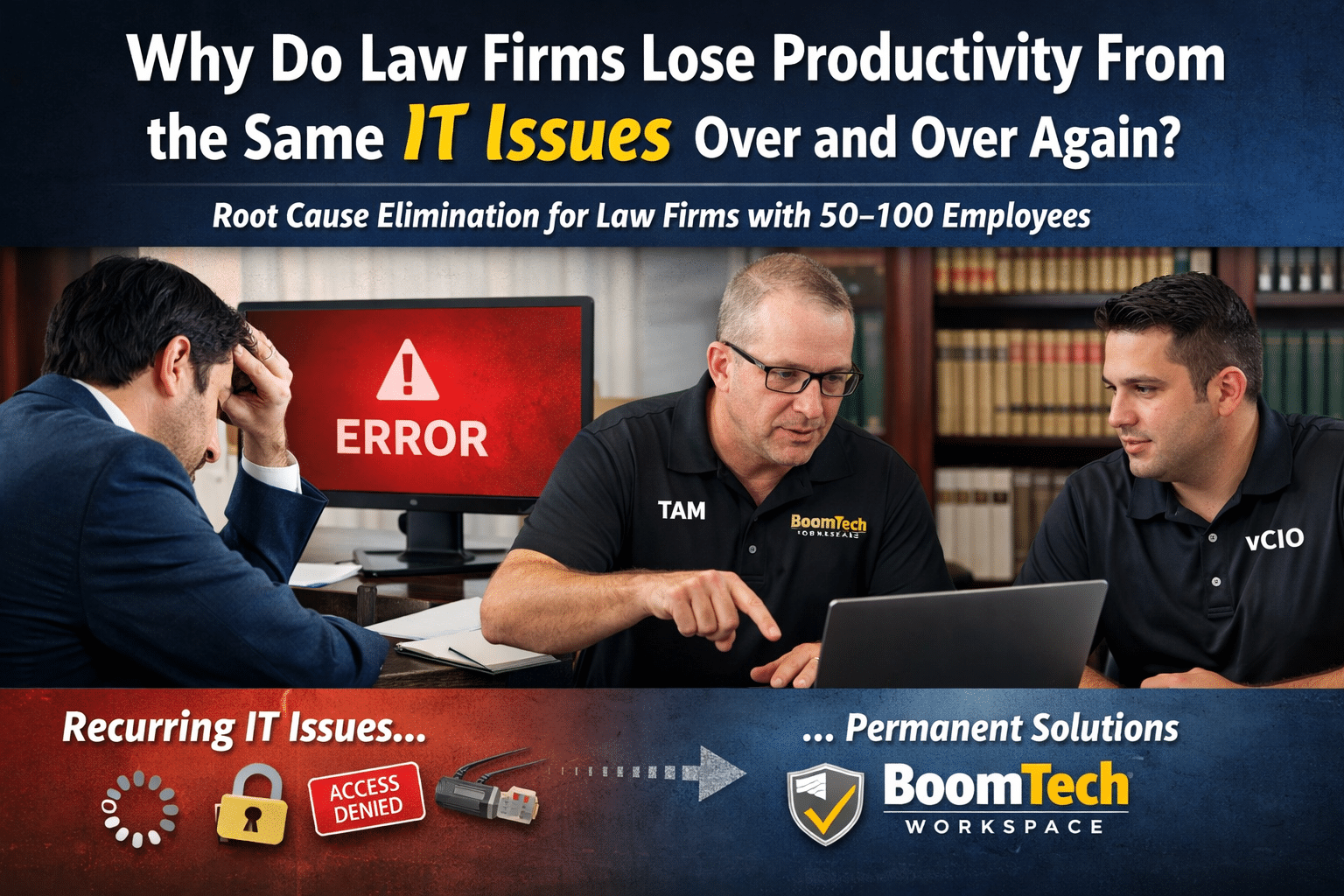
Read MoreWhy Do Law Firms Lose Productivity From the Same IT Issues Over and Over Again?
Law firms with 50–100 employees across multiple locations can lose 10+ hours per month in downtime from recurring technology problems. Even small IT disruptions—slow networks, document access issues, repeated password resets—add up fast when attorneys are billing by the hour. At BoomTech, we don’t just fix tickets. We eliminate the root cause permanently. What Recurring…
Read MoreHow Smart Tech Budgets Drive Business Growth — Not Just IT Performance
Reimagine Your IT Budget for Strategic Growth – Smart Tech Budgets When was the last time your IT budget was discussed as a strategic asset — rather than a necessary expense? At BoomTech, we help South Florida law firms, accounting practices, wholesale distributors, and auto dealerships shift this outdated mindset. Technology should fuel business growth,…
Read More